Incident Responder
Security operations · Incident response · On-call
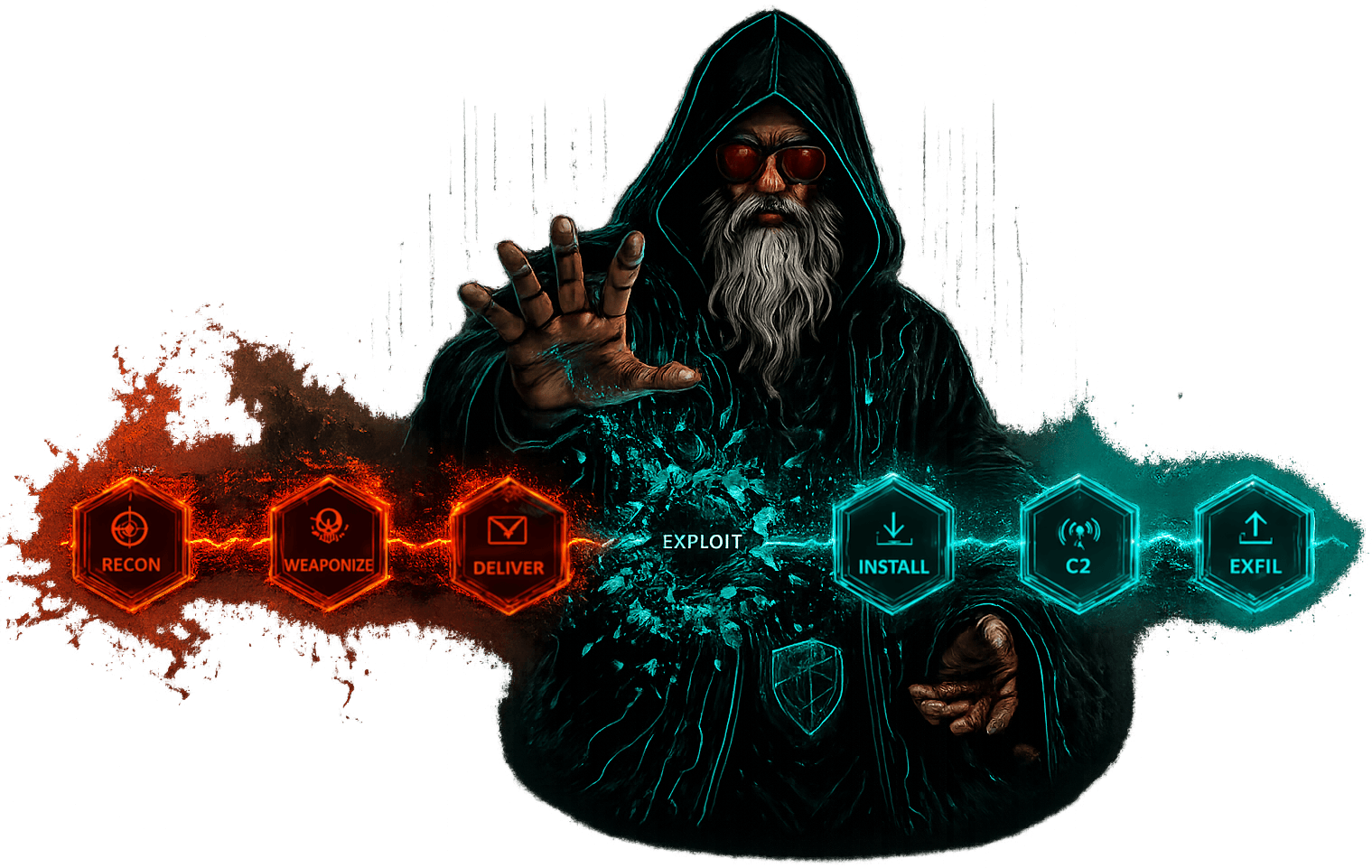
Stood watch while the forest burned. The pager went off at 3 a.m. and it didn't lie — attacker in the network, lateral movement confirmed, kill chain mid-flight. The work: trace the intrusion path, contain the breach, cut the next stage before it landed. Read packet captures like scripture, correlated logs across a dozen systems, and wrote post-mortems that asked the uncomfortable questions. Learned to think like the adversary so I could move faster.
DFIR Threat hunting Kill chain On-call Forensics